Market Shift: The Evolution of Password Security
The rise of automated systems for generating passwords has become a double-edged sword in the cybersecurity realm. On one hand, these advancements present new opportunities for efficiency and user experience. On the other hand, they also expose significant vulnerabilities that could be exploited by cybercriminals. According to a recent report by Cybersecurity Ventures, the global cybersecurity market is projected to reach $345.4 billion by 2026, driven largely by the increasing demand for robust security solutions. Yet, as organizations pivot towards automation, the reliance on imperfect password generation models could lead to a new wave of security breaches.
A study conducted by the International Journal of Information Security found that many leading password generation technologies, including those from major players like OpenAI and Google, are built on patterns derived from vast datasets. This reliance on training data introduces a critical flaw: the passwords produced often mimic strength while remaining vulnerable to sophisticated cracking techniques. For instance, passwords generated by models such as Claude may seem secure but are often predictable, leading to a false sense of security among users.
Understanding the Predictability Problem
The inadequacy of current solutions is further underscored by data showing that a sample of 50 passwords generated by Claude yielded only 23 unique variants. This alarming statistic highlights a significant issue: the predictability of these passwords undermines their effectiveness as security barriers. While some may tout the longevity of these passwords against brute-force attacks, the reality is that cybercriminals have access to advanced tools that can easily exploit the underlying patterns.
Moreover, as developers increasingly lean on automated systems for coding, the potential for embedding insecure passwords into applications grows. A recent analysis of popular code repositories revealed numerous instances of AI-generated passwords being incorporated into actual applications and services. This trend raises a red flag for developers and organizations alike, signaling the urgent need to reassess password practices to prevent inadvertent security lapses.
Second-Order Effects: The Ripple Impact on Cybersecurity
As organizations adopt automated password generation, the implications extend far beyond individual users. The second-order effects of relying on flawed password generation technology could reshape the cybersecurity landscape in profound ways.
Potential Backdoors and Increased Vulnerability
The integration of AI-generated passwords into codebases poses a significant risk of creating backdoors into sensitive systems. Cybersecurity experts emphasize that many developers may unknowingly incorporate these inadequately secured passwords into their applications, leading to potential exposure and exploitation by malicious actors. The historical precedent is clear; past breaches have often traced back to simple oversights in password management, underscoring the need for vigilance.
Moreover, as the industry grapples with these new vulnerabilities, the market may witness a shift in consumer trust. Users are becoming increasingly aware of cybersecurity threats, and any lapse in security could result in a loss of confidence in brands and services. This shift could drive organizations to invest more heavily in alternative authentication methods, such as biometrics and multi-factor authentication, ultimately reshaping the landscape of user authentication.
Data & Competition: Winners and Losers in the Cybersecurity Arena
As the cybersecurity market evolves, certain players are poised to benefit from the growing emphasis on secure password practices while others may find themselves at a disadvantage.
Winners: Innovative Security Solutions
Companies that prioritize the development of secure password generation mechanisms, such as those focusing on true randomness, are likely to thrive in this changing landscape. Firms that can effectively address the vulnerabilities inherent in current models stand to gain a competitive edge. For instance, cybersecurity firms specializing in biometric authentication and advanced encryption technologies are likely to see increased demand as organizations seek to bolster their security protocols.
Losers: Traditional Password Management Solutions
Conversely, firms that cling to outdated password management solutions without adapting to the evolving threats may face significant challenges. The reliance on AI-generated passwords that follow predictable patterns could lead to increased breaches and loss of consumer trust. Traditional password managers that fail to innovate may find themselves losing market share to more agile competitors offering advanced security features.
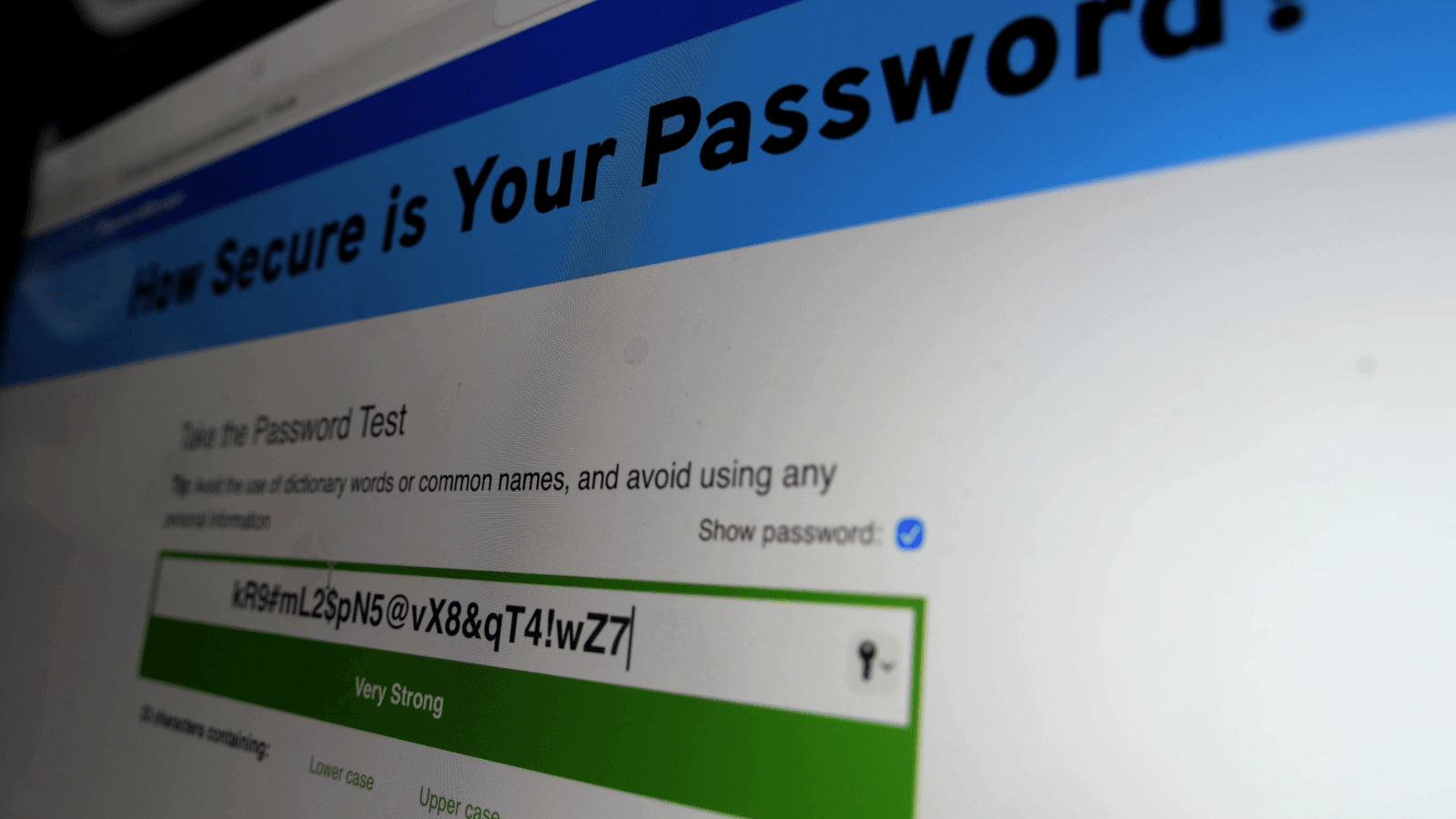
Why this visual matters: This visual illustrates the critical importance of password security and the evolving landscape of cybersecurity solutions. Understanding both password security and cybersecurity solutions is essential for organizations seeking to protect their digital infrastructure.
Core Execution Protocol: Immediate Action Steps
In light of these vulnerabilities, organizations must take decisive action to safeguard their operations. The core command is clear:
Frequently Asked Questions
What are the risks associated with AI-generated passwords?
AI-generated passwords often follow predictable patterns, making them vulnerable to cracking techniques employed by cybercriminals. This predictability can expose users and organizations to significant security risks.
How can organizations improve their password security?
Organizations can enhance their password security by auditing current password practices, implementing alternative authentication methods, and collaborating with cybersecurity experts to develop secure password generation tools.
What are the benefits of using biometric authentication?
Biometric authentication provides a higher level of security by relying on unique physical traits, making it more difficult for unauthorized users to gain access to sensitive information compared to traditional password methods.
Meet the Analyst
Marcus Vance, Tech Editor: With over a decade of experience in cybersecurity and technology journalism, Marcus provides in-depth analysis and insights into emerging trends and challenges in the digital landscape.
Last Updated: March 2026 | HustleBotics Editorial Team